IP Address Analysis Linked to 10.7.100.58 and Feedback
The IP address 10.7.100.58 signals a non-public RFC 1918 origin, indicating internal network segmentation and restricted exposure. Trace routes, logs, and responder telemetry form a closed feedback loop that informs topology, refines accuracy, and guides adaptive defenses. Patterns emerge around visibility, access controls, and containment timing, weighing privacy versus security. This data-driven approach offers rapid mitigation, but the implications for neutrality and disclosure warrant careful consideration as vulnerabilities and mitigations are weighed—and the next step becomes clear.
What 10.7.100.58 Tells Us About Network Footprints
What does the address 10.7.100.58 reveal about network footprints? The data indicates a non-public RFC 1918 origin, suggesting internal segmentation and access controls. Footprint analysis shows limited exposure, while network tracing corroborates constrained hops and private routing. This snapshot informs defenders and freedom-seekers alike about systemic visibility, emphasizing disciplined discovery without compromising operational neutrality or provoking unwarranted escalation.
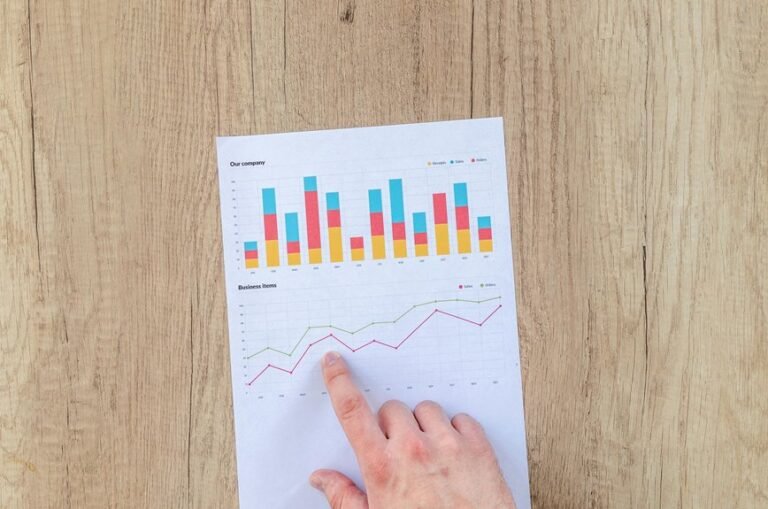
How Trace Routes, Logs, and Responders Create Feedback Loops
Trace routes, logs, and responders generate feedback loops by iteratively shaping and constraining network understanding: path measurements inform log interpretation, logs refine tracer outcomes, and responder behavior adapts in response to observed telemetry.
This dynamic exposes network footprints, quantifying perturbations and resilience.
trace routes, log responders, feedback loops, network footprints enable concise, data-driven assessment with minimal ambiguity.
Interpreting Patterns: Security Implications and Privacy Considerations
The analysis of patterns emerging from trace routes, logs, and responder telemetry informs security and privacy considerations by revealing how observable footprints can be exploited or concealed.
Patterns underscore privacy risks and the need for data minimization, ensuring minimal exposure while preserving analytic value.
Attribution concerns emerge, yet robust anomaly detection supports accountability without compromising confidentiality or user freedom.
Practical Incident Response: From Data to Faster Mitigation and Prevention
In practical incident response, data-driven workflows enable faster containment and prevention by translating telemetry from logs, traces, and responders into prioritized action plans.
The approach maps data patterns to network footprints and trace routes, enabling incident response refinement through feedback loops.
It weighs security implications and privacy considerations, guiding faster mitigation and prevention opportunities with clear mitigation strategies and actionable recommendations.
Conclusion
Conclusion:
The presence of 10.7.100.58 signals an internal, non-public RFC 1918 origin that constrains exposure while guiding visibility controls. Trace routes, logs, and responder telemetry form a closed loop: each data point informs the next, enabling rapid containment and prioritized action. Patterns emerge as data-driven indicators for anomaly detection and defense tuning. How can organizations further minimize privacy risks while preserving actionable insight to accelerate mitigation and prevention?